Turns out even government-owned drones aren't as secure as you'd think.
A security researcher at IBM has demonstrated at a conference just how easy it is to hack into a £25,000 professional police drone using nothing but £30 of off-the-shelf components.

Nils Rodday gave a talk and a live demonstration at the RSA Conference showing how with the right knowledge and a fairly common piece of equipment he could kick the drone pilot off the drone's WiFi network and then take control of it.
Rodday conducted much of his drone hacking while at the University of Twente in the Netherlands when a well-known professional drone company agreed to loan him one of their most advanced units in return for finding any vulnerabilities.
SEE ALSO:
What Rodday found was that the drone uses WEP (Wired-end encryption) to scramble the messages, unfortunately for this drone company (and many others), WEP is well known to be crackable in under a minute.
If that wasn't bad enough Rodday then found that the chip transmitting the radio signals was an off-the-shelf component called a Xbee which costs just $40.
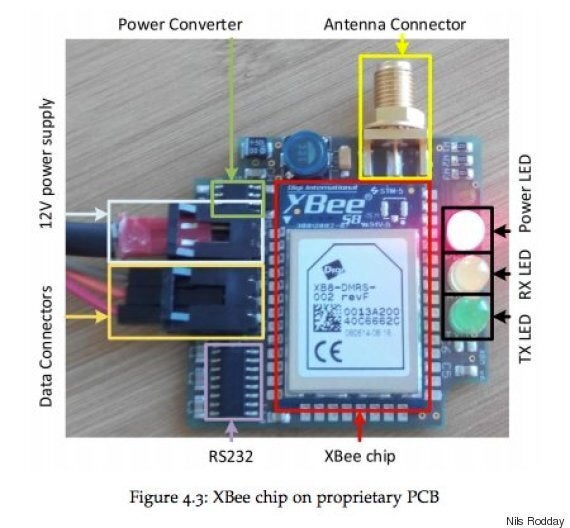
Xbee is normally encrypted, but to make sure that the drone's responsiveness is good enough the company removed the encryption entirely making it hugely vulnerable.
Rodday worries that these two weaknesses essentially give a hacker everything they need to take complete control of the drone.

“You can inject packets and alter waypoints, change data on the flight computer, set a different coming home position, everything the original operator can do, you can do as well.” he says.
While Rodday won't mention the name of the drone manufacturer there are a number of companies that offer medium-sized drones for surveillance, life-saving and military functionality to government agencies including the Police, armed forces and emergency services.
His fear is that not only is this vulnerability not exclusive to one manufacturer but that now they're out in the wild these drones cannot be protected through a simple software update.