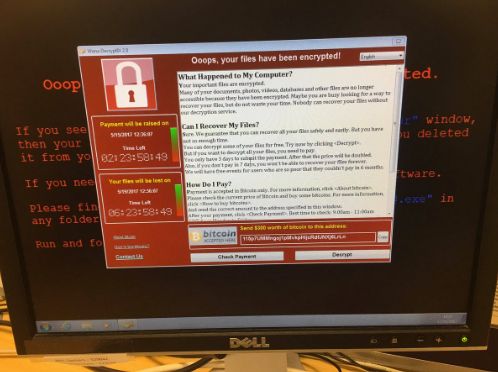
A cybersecurity researcher has revealed how he “accidentally” halted the spread of ransomware during the attack on hundreds of systems worldwide on Friday, including the NHS.
The health service faces a weekend of backlog after a debilitating cyber attack prompted hospitals to cancel and delay treatment for patients across the country on Friday.
The researcher, who tweets as @MalwareTechBlog, is thought to have located and inadvertently activated a “kill switch” in the malicious software, with the help of Darien Huss from security firm Proofpoint.
MalwareTech is reportedly 22 years old and lives with his parents in south-west England.
While analysing the code behind the malware, the researcher, who wants to protect his identity, noticed that the malware was trying to contact a web address that was not connected to a website as it has not been registered.
MalwareTech decided to spend £8.50 and claim the web address, thereby allowing him access to the analytical data and get an idea of how widespread the ransomware was.
“The intent was to just monitor the spread and see if we could do anything about it later on. But we actually stopped the spread just by registering the domain,” he told the Guardian.
The following hours were an “emotional rollercoaster”.
“Initially someone had reported the wrong way round that we had caused the infection by registering the domain, so I had a mini freakout until I realised it was actually the other way around and we had stopped it,” he said.
On Saturday Home Secretary Amber Rudd urged NHS trusts to upgrade their computer systems after it was reported that 90% of NHS hospitals are still using Windows XP.
Rudd said that invetsigators still do not know where the attack came from but that it “wasn’t targeted at the NHS”.
The National Cyber Security Centre (NCSC) has said Friday’s incident was part of a set of global cyber attacks against “thousands of organisations and individuals in dozens of countries” as it launched a major operation in response.
The Home Secretary said that patient data is secure and that no patient data has been accessed or transferred “in any way”.
At least 30 health service organisations in England and Scotland were infiltrated by the ransomware, while many others shut down servers as a precautionary measure, bringing added disruption yesterday afternoon.
