First, experts warned internet users to change all of their passwords in the wake of the devastating Heartbleed bug.
Then they didn't.
So who do you believe?
Finally, some consistent advice has started to emerge following the discovery of the flaw in OpenSSL, the tech which runs much of the encrypted web. The Heartbleed bug was discovered on Monday by a team of security experts, including one from Google, having gone undetected for more than two years.
The bug bypasses the encryption that normally protects data as it is sent between computers and servers, leaving personal and sensitive data vulnerable. It is commonly recognised as the closed padlock that appears in the corner of the web browser to show your connection is secure.
There is also now evidence that hackers were probing sites for the bug before it was publicly announced - indicating hackers may have had a headstart in gathering sensitive data. Up to 500,000 servers could be affected - and all need to be manually patched to fix the bug.
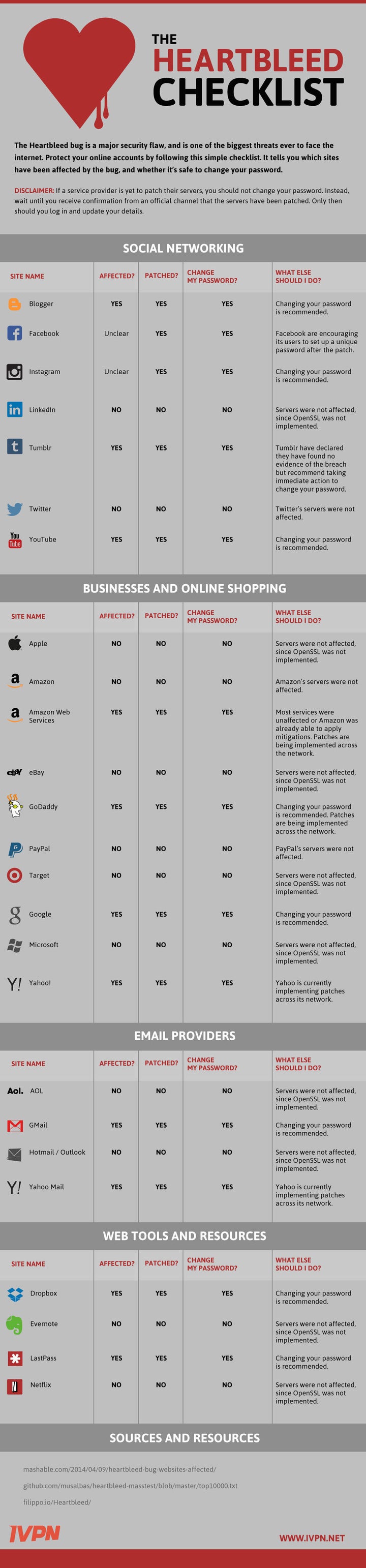
Experts are starting to agree that the best way to deal with the issue is to change the passwords for affected websites only, and only once they've fixed the bug.
Here are some of the key highlights:
- AOL Email: not affected
- Yahoo Mail: affected, fixed, change your password
- Facebook: unclear if affected, but you should change your password
- Instagram: affected, change your password
- Linked In: Not affected
- Tumblr: affected, change your password
- Twitter: not affected, but patch applied
- Apple: not affected
- Amazon: not affected
- Google: affected, fixed, probably change your password
- Microsoft: not affected
UK experts agree that users should put in the leg work to find out which of their services were affected, and change their passwords accordingly.
"Change your passwords - but only after the affected website operators and internet service providers have implemented the patch to fix the bug," said Hugh Boyes, cyber security lead at the UK-based Institution of Engineering and Technology.
"Changing your password before the bug is fixed could compromise your new password."
