The global cyber attack which crippled NHS services on Friday could strike again as people return to work today, experts have warned.
More than 200,000 victims in around 150 countries have been infected by the ransomware which originated in the UK and Spain on Friday before spreading globally.
Ciaran Martin, chief executive of the National Cyber Security Centre, said the outbreak could continue to infect more systems and other victims may emerge.
“On Monday morning at the start of the new working week it’s likely that successful attacks from Friday that haven’t yet become apparent will become apparent,” he said.
“And also existing known infections can spread, we can’t say what scale the new cases will occur at but it’s likely there will be some.”
Japanese companies earlier raised alarms, with big brands admitting their systems had been affected.
Hitachi said it was experiencing email delays and file delivery failures and suspected the cyber attack was to blame, even though no ransom was being demanded. It said programmes were being installed to fix the problem.
And the blogger who helped halt the spread of the ransomware said yesterday a second wave of attacks could begin as businesses reboot their systems.
It is not known how the attack has affected GP surgeries, which are due to open as usual on Monday, the Press Association reported.
An NHS England spokesman described it is a “very complex emerging picture”.
People are advised to attend any hospital or doctor appointments as normal, unless they are contacted and told not to.
Professor Helen Stokes-Lampard of the Royal College of General Practitioners said many GPs went into their practices on Sunday to reboot their computers and install updates.
“GPs, of course, can still diagnose and treat patients without using computers but we ask our patients to bear with us if routine services such as repeat prescriptions and appointment booking services are slightly disrupted this week,” she said.
“In the meantime, we wish to reassure patients that your GP will be there for you as usual if you are taken ill and that you will receive the best possible care from the NHS, despite the current difficulties.”
Around a fifth of NHS trusts were hit in the attack, forcing them to postpone operations and procedures over the weekend.
Seven hospitals remained on A&E divert on Sunday afternoon, with ambulances taking emergency patients elsewhere, NHS England said.
Dr Anne Rainsberry, NHS incident director, said: “We have been working with 47 organisations providing urgent and emergency care who have been infected to varying degrees.
“Most have found ways of working around this but seven, including St Barts in London, have asked for extra support.”
It comes amid concerns networks were left vulnerable because they were still using outdated Windows XP software.
Brad Smith, Microsoft president and chief legal officer, described what happened as a “powerful reminder” of the importance of updating software.
“The fact that so many computers remained vulnerable two months after the release of a patch illustrates this aspect,” he said in a blog post.
“As cybercriminals become more sophisticated, there is simply no way for customers to protect themselves against threats unless they update their systems.
“Otherwise they’re literally fighting the problems of the present with tools from the past.”
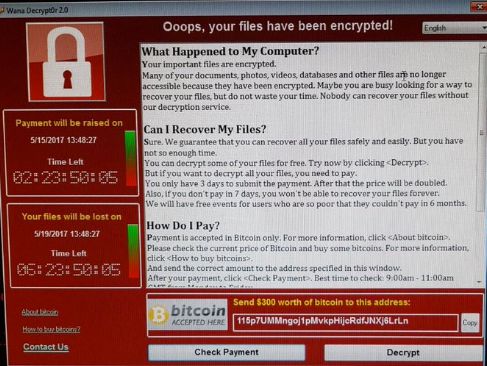
Medical staff reported seeing computers go down “one by one” as the Wanna Decryptor ransomware, also known as WannaCry, took hold, locking machines and demanding money to release the data.
The apparent chink in the NHS’s defences led to criticism of the Government, with the Liberal Democrats demanding an inquiry.
Labour’s shadow health secretary, Jonathan Ashworth, in a letter to Health Secretary Jeremy Hunt, said concerns were repeatedly flagged about outdated computer systems.
Investigators from around the globe, including the National Crime Agency, are working to hunt down those responsible for the virus.
A British cyber whiz was hailed an “accidental hero” after he registered a domain name that unexpectedly stopped the spread of the virus.
The anonymous specialist, known only as MalwareTech, issued a warning that hackers could upgrade the virus to remove the kill switch.
Among those affected by the virus was Nissan, but the car manufacturer said there had been no major impact.
A spokesman said it was “business as usual” for the Sunday night production shift at the plant in Sunderland.