A major cyberattack took place over the weekend, it was targeted at a company called Dyn and while you’ve probably never heard of them until now, the likelihood is that you felt the effects.
The attack knocked out Spotify, Twitter, Amazon and even Netflix for hours with huge outages reported on a global scale.
For many security companies it’s their worst fears realised as it marks the first major instance where hackers have taken control of our smart home gadgets, and used them as a weapon.

So what actually happened?
It was something called a Distributed Denial of Service Attack (DDoS), where hackers overload a website’s servers by sending unimaginably large amounts of traffic at it.
A great example is when you buy Glastonbury tickets: Every year the site crashes and ceases to function. It does this because there are more people trying to access it then can be managed.
In a DDoS attack, hackers will drive traffic like a battering ram towards the intended site and in doing so slow it down to the point of being useless.
To do this hackers will normally use either their own computing power or enlist other computers to send traffic by illegally taking them over with viruses.
This wasn’t a normal attack though, the scale of it was enormous.
To do this hackers utilised a powerful new piece of malware called Mirai. Mirai is incredibly dangerous for one simple reason, which is that it takes advantage of the Internet of Things.

So many household items we own now use the internet in some way: smart fridges, security cameras, baby monitors and even your washing machine.
Very few of these devices are really that protected, so what Mirai does is hijack them and start forcing them to send huge volumes of traffic to the target.
Why were so many websites affected?
What happened this weekend was different to normal DDoS attacks. Normally criminals or state-backed hackers will target a single company or organisation.
In this instance, the attackers went after a company called Dyn, a DNS provider which effectively acts as the switchboard for many of the world’s biggest tech companies.
When you type in Twitter.com, Dyn is there making sure you end up going to the right site.
Unfortunately this makes Dyn an incredibly lucrative target, because if you hit the switchboard, then all the sites go down. This is one of the first times that an attack has been carried out in this fashion.
How can you protect yourself?
The truth is you won’t be able to stop hackers from knocking out Twitter or Spotify using DDoS attacks. What you can do though is both slow them down and also protect your home gadgets from being turned into a cybercriminals newest toy.
Here are 7 great tips from Chester Wisniewski at Sophos Security on how to protect your home:
Many smart things support Wi-Fi so that you don’t have to plug them into your smartphone or computer every time you want to use them. If your home Wi-Fi router allows you to create separate guest networks to keep untrusted visitors off your regular network, make a special guest network for your “things” and connect them there.
Many devices, such as video cameras, try to talk to your router to open up inbound holes so they can accept connections from outside. This makes it easier to access them from the internet, but it also exposes your devices to the rest of the world. Turn off Universal Plug and Play (UPnP) on your router, and on your IoT devices if possible, to prevent this exposure. Don’t assume that “no one will notice” when you hook up your device for the first time. There are specialised search engines that go out of their way to locate and index online devices, whether you wanted them to be found or not.
Keep the firmware up to date on all of your IoT devices – patching is just as important as it is on your PC. It can be time consuming to figure out whether updates are available, but why not make a habit of checking the manufacturer’s website twice a year? Treat it like changing your smoke detector batteries: a small price to pay for safety and security.
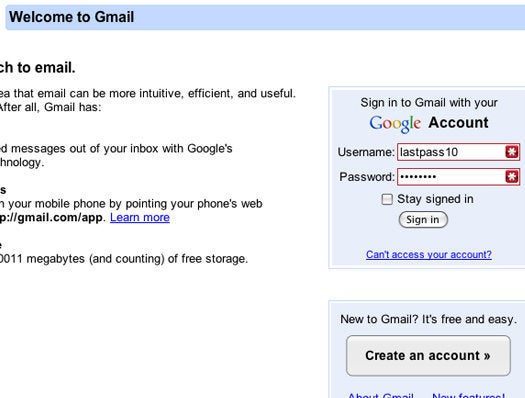
Choose passwords carefully and write them down if needed. Complexity is important, but so is uniqueness. Many IoT devices have been found to have bugs that let attackers trick them into leaking security information, such as giving away your Wi-Fi password. Remember: one device, one password.
Favor devices that can work without the cloud. IoT “things” that require a cloud service are often less secure, and potentially give way more information, than those you can control entirely from within your home. Read the packaging carefully to determine whether permanent internet access is needed for the device to function. If it’s “all-or-nothing,” then you can’t try out the device on your own network first.
Only network devices as much as you need to. If all you want from your TV is to watch broadcast television, you don’t need to connect it to the network at all. If you only want to control it or stream to it from your home network, it doesn’t need access to or from the outside. Eliminate unnecessary internet connections when possible.
Don’t take your IoT devices to work or connect them to your employer’s network without permission from IT. Insecure devices could be used by attackers as a foothold into the organisation, and used to assist with data stealing and illicit surveillance. You could put your company and your job at risk.
Best Password Managers: