Thousands of National Lottery accounts may have been hacked, reports its operator Camelot.
In a statement on its website, the operator said that it had detected suspicious activity within some of its accounts and investigated.
It now believes that around 26,500 accounts could be compromised with around 50 reporting unauthorised activity.

This was not a hack of the National Lottery’s core network or its systems however, instead it’s believed that the accounts were accessed through stolen login information that was being made available on another website.
Of the 50 affected Camelot says that no money was stolen however by gaining access to these accounts the hackers will have seen personal information.
Camelot is now contacting the accounts that it believes are affected and is helping those users re-secure their accounts with new login information.
With over 9.5 million registered players, 26,500 makes up a very small number of Camelot’s total players and with only 50 accounts accessed the damage could be quite small.
That being said this is just the latest in a long stream of hacking incidents in which criminals were either able to access a company’s core systems or get hold of vast swathes of usernames and passwords effectively handing them access to people’s accounts.
Security experts have commended Camelot on their security systems and their swift response to this incident.
James Maude, senior security engineer at global cyber security expert Avecto said: “Camelot has moved quickly in responding to this breach, locking down accounts, triggering compulsory password resets and contacting for those affected directly. That has to be commended, unfortunately most companies aren’t quite so vigilant.”
Andy Herrington, Head of Cyber Professional Services in UK & Ireland at Fujitsu added: “It appears to be very much a pro-active statement which seeks to re-assure users by providing details of the incident in a very controlled way which is easy to understand. The fact that Camelot’s monitoring systems have played a clear role and that they have been able to investigate the incident, threat vector and impact quickly also demonstrates a level of maturity and control.”
How were the accounts hacked?
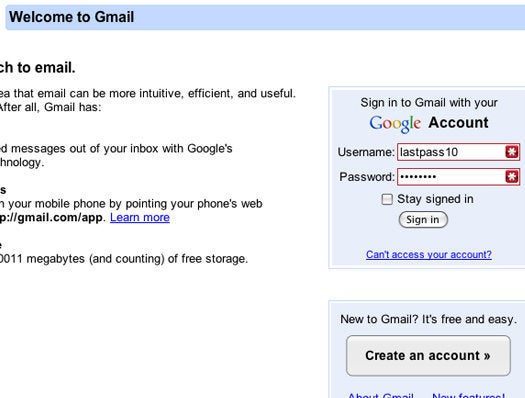
“This is part of a continuing trend of credential stuffing, where passwords from one breach are reused to gain access to other accounts to harvest more personal information. Users need to be aware of the dangers of reusing passwords especially when these cross the boundary between personal and business accounts.” explains Maude.
This story is developing...
Password Managers to create an unbreakable password: