Android malware is now coming right out and demanding money from its victims.
Reports are emerging that so-called 'ransomware' is asking victims to pay fines with messages purporting to come from law enforcement agencies.
Luckily it doesn't seem possible to install the malware, officially named Android.Trokan.Koler.A, without actually asking it to install on your phone.
Unluckily, it does this in the guise of a driver that is needed to watch porn films.
Once you've granted the app permission to install, though, you're in trouble. The app sends the IMEI number of your smartphone back to the gang running it, as well as the nearest location it can determine based on your GPS settings.
It then displays a message on your phone claiming to be from the FBI Department of Defense, the 'USA Cyber Crime Centre' or even the Metropolitan Police (complete with a picture of the Queen). Presumably the image of the monarch is supposed to inspire a new level of fear and intimidation within the intended victim.
The message says:
"You are accused of viewing/storage and/or dissemination of banned pornography (child pornography/zoophilia/rape etc). You have violated World Declaration on non-proliferation of child pornography. You are accused of committing the crime envisaged by Article 161 of United States of America criminal law."
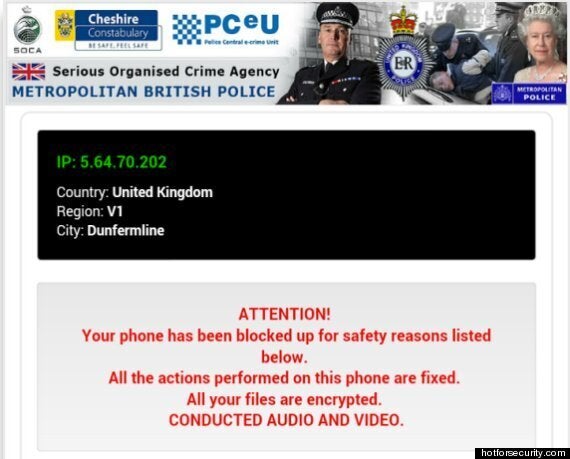
Then it does the inevitable, and sends you a message demanding $300 or it will "encrypt your files" - something it cannot do.
It's easy enough to uninstall - just drag the app up to the notifications tray and uninstall it in the usual way. But unless you know what you're looking at, it could be quite scary.
Some experts said that it was not important to over-react, but said users should take obvious steps to protect themselves - like not downloading dodgy drivers from 'adult' sites.
Michael Sutton, vp of security research at Zscaler, said in an email:
"Koler is also a pure social engineering attack, tricking the user into installing the application. In short, it's not a particularly sophisticated piece of malware. It's new and and I do not expect it to become a major threat, given the lack of sophistication but it may also be a first step to experiment in the Android space, leveraging a technique that has been rather profitable in the PC world."