Cybersecurity
From secretly snapped feet pics to love letters to colleagues, tech workers find some pretty strange stuff on company computers.
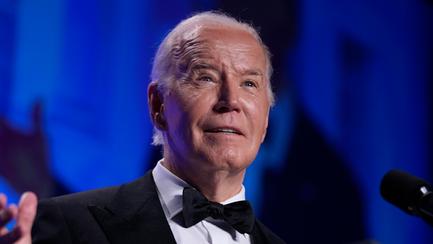
"We're on the verge of what I fear to be a pretty significant breakdown in democracy and civil society," said Chris Krebs.
Chris Krebs' federal agency wouldn't back up the president's allegations that voting in the 2020 election was compromised.
Yes it's boring, but here's a reason to update your computer.
The hack could reveal the identity of users who wish to remain anonymous.
Almost six million bank details were hacked as well.
You could be more at risk than you realise.
This will change your life.
The message looks like it has come from a contact.
This affects almost every gadget you own.